TL;DR:
- Americans lost over $12.5 billion to fraud in 2024, targeting all age groups equally.
- Online fraud includes phishing, shopping scams, imposter schemes, investment fraud, and identity theft.
- Vigilance, verifying sources, and building safe habits are more effective than relying solely on technical tools.
Americans lost over $12.5 billion to fraud in 2024 alone, and most of those victims were not careless or naive. They were ordinary people, checking their phones before breakfast or shopping online after work. Online fraud does not discriminate. It targets grandparents, college students, small business owners, and busy parents equally. This guide breaks down exactly what online fraud is, how it works, and what you can do right now to protect yourself and everyone in your household, without needing a tech background to follow along.
Table of Contents
- Common types of online fraud you should know
- How online fraud actually works: tactics and triggers
- Why payment is not the only danger: identity and data theft
- Practical protection: easy steps for everyday safety
- Why everyday vigilance beats technical tools for families
- Get extra protection: tools and resources from ScamKit
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Fraud is widespread | Online scams cause billions of dollars in losses each year and affect millions of people. |
| Scammers use pressure | Fraudsters rely on urgency, fear, and impersonation to trick victims into fast mistakes. |
| Data theft matters | Online fraud includes identity and account theft, not just direct payment scams. |
| Simple steps work | Verifying messages and avoiding suspicious links are the most effective family protections. |
| Tools can help | Reliable online resources assist with checking links, emails, and tracking scam patterns. |
Common types of online fraud you should know
Online fraud is not one single thing. It shows up in many different forms, and scammers are constantly finding new angles. Understanding the main categories helps you recognize danger before it costs you money or your personal information.
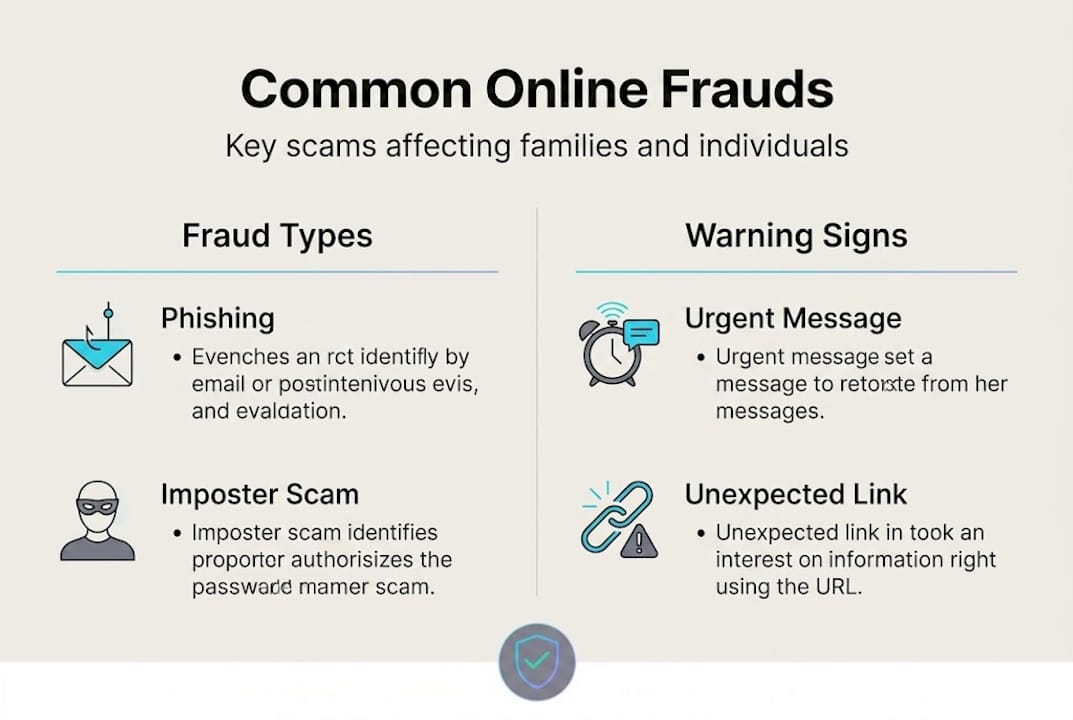
Fraud types like imposter scams and internet shopping fraud consistently rank among the most reported categories in consumer data. Here is a breakdown of what each one looks like in real life.
Phishing scams
Phishing is when a scammer sends you a message, usually an email or text, pretending to be someone you trust. The message might look like it came from your bank, the IRS, or even Amazon. The goal is to get you to click a link and hand over your password, credit card number, or Social Security number. Learning to spot fake links before you click is one of the most valuable skills you can build. For a closer look at what these messages actually look like, phishing email examples can help you recognize the warning signs fast.
Online shopping fraud
You find a great deal on a product, pay for it, and it never arrives. Or the item shows up and it is nothing like what was advertised. Fake online stores are everywhere, especially on social media. Some scammers set up entire websites that look legitimate, complete with product photos and fake reviews, just to steal your payment information.
Imposter scams
This is when someone pretends to be a government official, a bank employee, a family member in trouble, or even a romantic interest. Imagine getting a call from someone claiming to be your grandchild, saying they are in jail and need money wired immediately. That panic you feel? That is exactly what the scammer is counting on.
Investment and crypto scams
These scams promise huge returns on investments, often involving cryptocurrency. The pitch sounds professional and the fake websites look polished. But once you send money, it disappears. These scams have exploded in recent years and are now one of the costliest fraud categories for adults over 60.
Account and identity theft
This happens when someone gets hold of your login credentials and takes over your accounts. They might drain your bank account, lock you out of your email, or use your identity to open new credit lines. Check out current popular scams to see what is actively targeting people right now.
| Fraud type | Common delivery method | Primary goal |
|---|---|---|
| Phishing | Email, text, fake websites | Steal credentials or personal info |
| Online shopping fraud | Social media ads, fake stores | Steal payment or ship nothing |
| Imposter scams | Phone calls, texts, email | Pressure victim into sending money |
| Investment/crypto scams | Social media, fake platforms | Steal investment funds |
| Identity/account theft | Data breaches, phishing | Access accounts, open credit lines |
"Online fraud is not always dramatic. Sometimes it starts with a single email that looks completely normal."
How online fraud actually works: tactics and triggers
Knowing the types of fraud is step one. Understanding how scammers actually pull it off is where things get really eye-opening. Most online fraud does not succeed because of technical wizardry. It succeeds because of psychology.
The FTC warns that scammers are specifically trained to make you panic and act quickly, before you have time to think clearly. That urgency is the weapon.
Here is how the typical scam unfolds, step by step:
- You receive an unexpected message. It could be a text saying your bank account is locked, an email claiming you owe the IRS money, or a social media message from a "friend" in trouble.
- The message creates pressure. Words like "Act now," "Your account will be closed," or "You have 24 hours" are designed to short-circuit your judgment.
- You are directed to take a specific action. This might be clicking a link, calling a number, downloading an attachment, or sending a payment.
- The scammer collects what they need. Whether that is your password, a verification code, or a wire transfer, once they have it, the damage is done.
Understanding common scam techniques helps you recognize these patterns before you get pulled in.
The psychological triggers scammers rely on most:
- Urgency: "You must respond within the hour."
- Fear: "Your account has been compromised."
- Authority: "This is the Social Security Administration."
- Sympathy: "I'm stranded and need help."
- Greed: "You've been selected for an exclusive investment opportunity."
Each of these triggers bypasses your rational thinking and pushes you toward a fast, emotional reaction. That is the entire strategy.
Pro Tip: Before you respond to any unexpected message, pause for 60 seconds. Ask yourself: "Did I initiate this contact?" If the answer is no, treat it as suspicious until proven otherwise. That one habit alone can stop most scams cold.
| Trigger used | Example phrase | Intended reaction |
|---|---|---|
| Urgency | "Act within 24 hours" | Rush without thinking |
| Fear | "Your account is suspended" | Panic and comply |
| Authority | "This is the IRS" | Automatic trust |
| Sympathy | "I'm in danger, please help" | Emotional override |
| Greed | "Guaranteed 300% returns" | Excitement clouds judgment |
For a deeper look at protecting yourself day to day, practical scam prevention steps walks through what actually works.
Why payment is not the only danger: identity and data theft
Most people think of online fraud as someone stealing their credit card number. That is a real risk, but it is only part of the picture. Cyber-enabled fraud frequently involves identity theft and account takeover, not just direct requests for money. If you are only watching out for payment scams, you are missing a significant part of the threat.
Here is why identity and data theft can actually be more damaging in the long run:
- Account takeover: A scammer gets into your email or bank account and changes your password. Now you are locked out while they drain funds, read your messages, or impersonate you to your contacts.
- Credential stuffing: If you use the same password across multiple sites and one gets breached, attackers try that password everywhere. One stolen password can unlock many accounts.
- Synthetic identity fraud: Scammers combine your real information, like your Social Security number, with fake details to create a new identity. They then open credit accounts in that fake name, and you may not find out for months or years.
- Targeted phishing: Once scammers have some of your personal data, they use it to craft more convincing follow-up attacks. A scammer who knows your bank's name can send you a very believable phishing email.
"The most dangerous scams are the ones you do not realize happened until the damage is already done."
Social media scams are a particularly common entry point for identity theft. Scammers use fake profiles, quizzes, and contests to collect personal details that seem harmless individually but add up to a full profile of who you are.
Students and young adults are also frequent targets. Student scam examples show how fake scholarship offers, financial aid fraud, and job scams specifically target people who are new to managing their own finances and may not yet know what to watch for.
Pro Tip: Set up account alerts with your bank and email provider. If someone logs in from an unusual location or changes your password, you want to know immediately, not days later.
Signs your identity may have been compromised:
- You receive bills or collection calls for accounts you never opened
- Your credit score drops suddenly without explanation
- You are locked out of an account you use regularly
- You stop receiving expected mail or bills
- You see unfamiliar charges on your bank or credit card statements
If any of these happen, act fast. The sooner you respond, the better your chances of limiting the damage.
Practical protection: easy steps for everyday safety
Now that the risks are clearer, here are simple, practical steps anyone can follow to stay safe. You do not need to be tech-savvy. You just need a few consistent habits.
The FTC recommends treating unexpected messages as suspicious by default, avoiding clicking links or opening attachments in those messages, and always contacting companies using contact information you already know is real, not information provided in the suspicious message itself.
Your everyday protection checklist:
- Treat every unexpected message, call, or email as suspicious until verified
- Never click links in messages you were not expecting, even if they look official
- Do not download attachments from unknown senders
- Never share verification codes with anyone, even someone claiming to be from your bank
- Use strong, unique passwords for every account and a password manager to keep track
- Turn on two-factor authentication wherever it is available
- Regularly check your bank and credit card statements for unfamiliar charges
For online shopping specifically, the FTC recommends researching sellers before buying, keeping records of your transactions, and using credit cards whenever possible because they offer charge dispute protections. If a seller only accepts gift cards, wire transfers, or cryptocurrency, that is a major warning sign. Walk away.
Here is a step-by-step approach for verifying any suspicious message:
- Do not click anything. Close the message or put your phone down.
- Find the real contact information. Go directly to the company's official website by typing it into your browser, or use a phone number from a statement you already have.
- Call or message the company directly. Ask if they actually sent the message you received.
- Report the suspicious message. Forward phishing emails to reportphishing@apwg.org or report scams at ReportFraud.ftc.gov.
- Delete the original message once you have confirmed it is a scam.
Learning to stop smishing and text scams is especially important right now, since text-based fraud has surged in recent years. And for a broader look at staying safe, scam avoidance best practices covers the full range of habits that make a real difference.
Pro Tip: When in doubt, call the company directly using a number you find yourself. Never use a phone number included in a suspicious message. Scammers can put any number they want in a text or email.
Why everyday vigilance beats technical tools for families
Here is something the cybersecurity industry does not always say out loud: most families do not get scammed because they lack the right software. They get scammed because they were in a hurry, or they trusted something that felt familiar, or they were caught off guard during a stressful moment.
Technical tools matter. A good URL checker, a reliable spam filter, and strong antivirus software all add real protection. But they are a safety net, not a substitute for judgment. And scammers know this. They design their attacks to pass technical filters and exploit human instinct instead.
The families who consistently avoid scams are not necessarily the ones with the best tech setup. They are the ones who have built a culture of skepticism and verification. They ask questions. They slow down. They check before they click. They talk to each other about suspicious messages instead of handling them alone.
Building safer digital habits is genuinely more powerful than any single tool you can install. A teenager who knows how to spot a phishing link protects the whole household. A grandparent who knows to call their grandchild back on a known number before wiring money stops a scam in its tracks.
The uncomfortable truth is that most fraud prevention advice focuses on what to do after something goes wrong. The real opportunity is before that moment. It is in the pause before you click, the habit of verifying, and the willingness to feel a little inconvenienced in exchange for staying safe. That is not a technical skill. It is a mindset. And it is one that every member of your family can develop, starting today.
Get extra protection: tools and resources from ScamKit
Staying informed is powerful, but having the right tools makes protection even easier. ScamKit was built specifically for people who want fast, reliable answers without needing a cybersecurity degree.
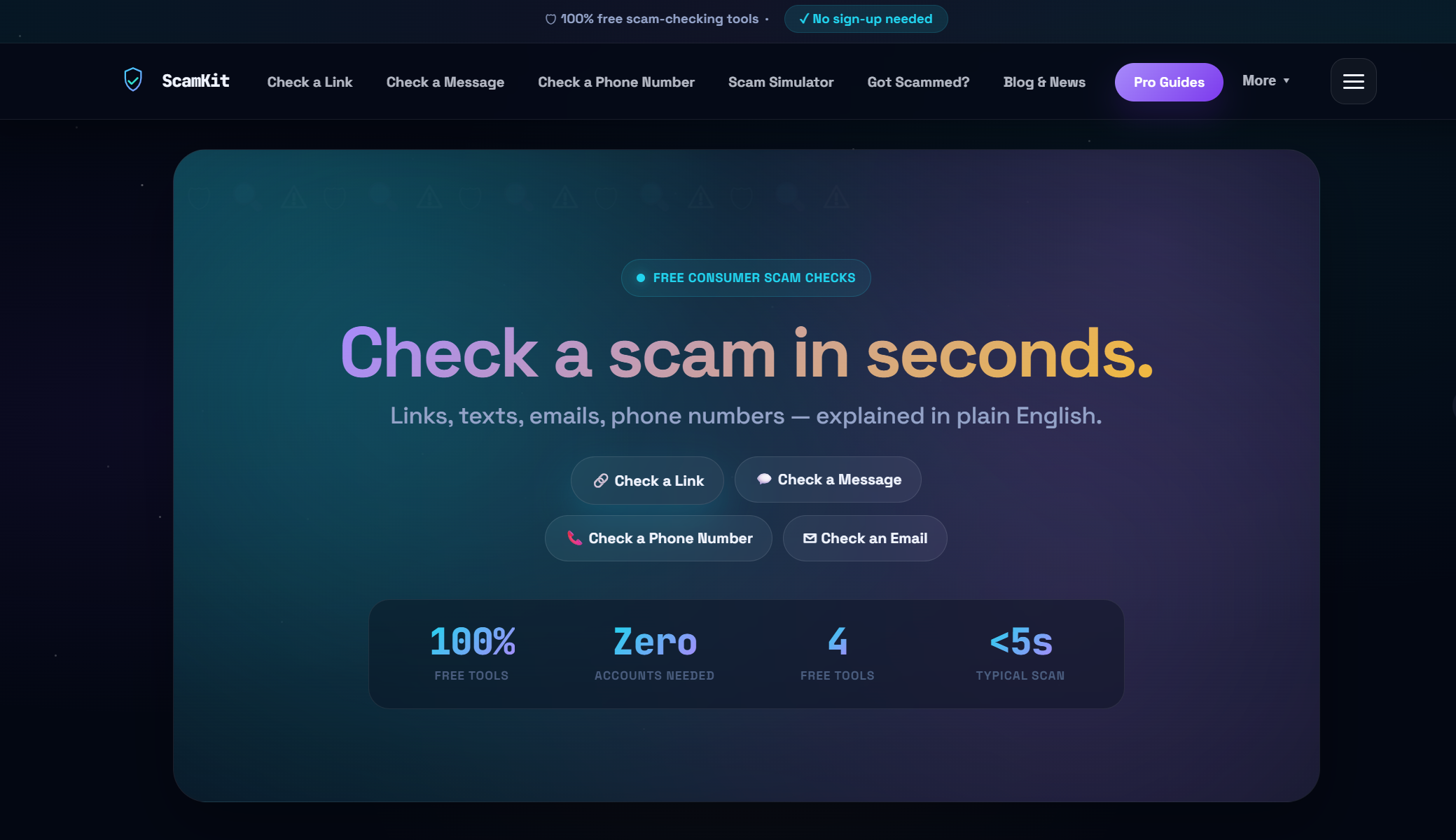
If you receive a suspicious link, run it through ScamKit's URL risk checker before you click. It analyzes the link instantly and gives you a clear risk rating. Got a strange email and not sure if it is real? The email scam analyzer can help you figure that out in seconds. And if you want to go further and build stronger habits for your whole household, ScamKit's guide to proactive cybersecurity walks you through what it means to stay ahead of threats rather than just react to them. No sign-up required. No personal data collected. Just fast, free protection when you need it most.
Frequently asked questions
How can I tell if a message is a scam?
Scam messages almost always create urgency or fear, ask you to share a verification code, or pressure you to send money fast. When in doubt, contact the sender directly using a phone number or website you already know is real.
Is paying with a credit card safer for online shopping?
Yes. Credit cards offer dispute protections that allow you to challenge fraudulent charges, which is something gift cards, wire transfers, and cryptocurrency do not provide.
What should I do if my identity is stolen online?
Contact your bank immediately, change all affected passwords, and report the theft to the FTC at IdentityTheft.gov. Because cyber-enabled fraud can involve account takeover and ongoing impersonation, acting quickly limits how much damage can be done.
Can scammers target children or students online?
Absolutely. Imposter scams and fake offers targeting students through fake scholarships, job listings, and financial aid fraud are increasingly common. Talking to younger family members about these tactics is one of the best protective steps you can take.
Should I trust links from unknown senders?
No. Always treat links from unknown senders as high risk. Avoid clicking links in unexpected messages and use a tool like ScamKit's URL checker to analyze any link you are unsure about before opening it.
